What Is ZEROBASE (ZBT)? A Complete Guide to Its on-chain Data Infrastructure and Decentralized Computing Model
In traditional Web3 architecture, data processing and computing capacity often depend on centralized services, making it difficult to balance transparency with privacy protection. By introducing zero knowledge proofs and trusted execution environments (TEE), ZEROBASE makes the computation process verifiable without exposing the underlying data, helping fill a critical gap in trusted on-chain data processing.
From a broader blockchain infrastructure perspective, ZEROBASE is not only a data processing network, but also an important bridge connecting privacy computing, compliance needs, and decentralized execution, providing foundational support for the next generation of Web3 applications.
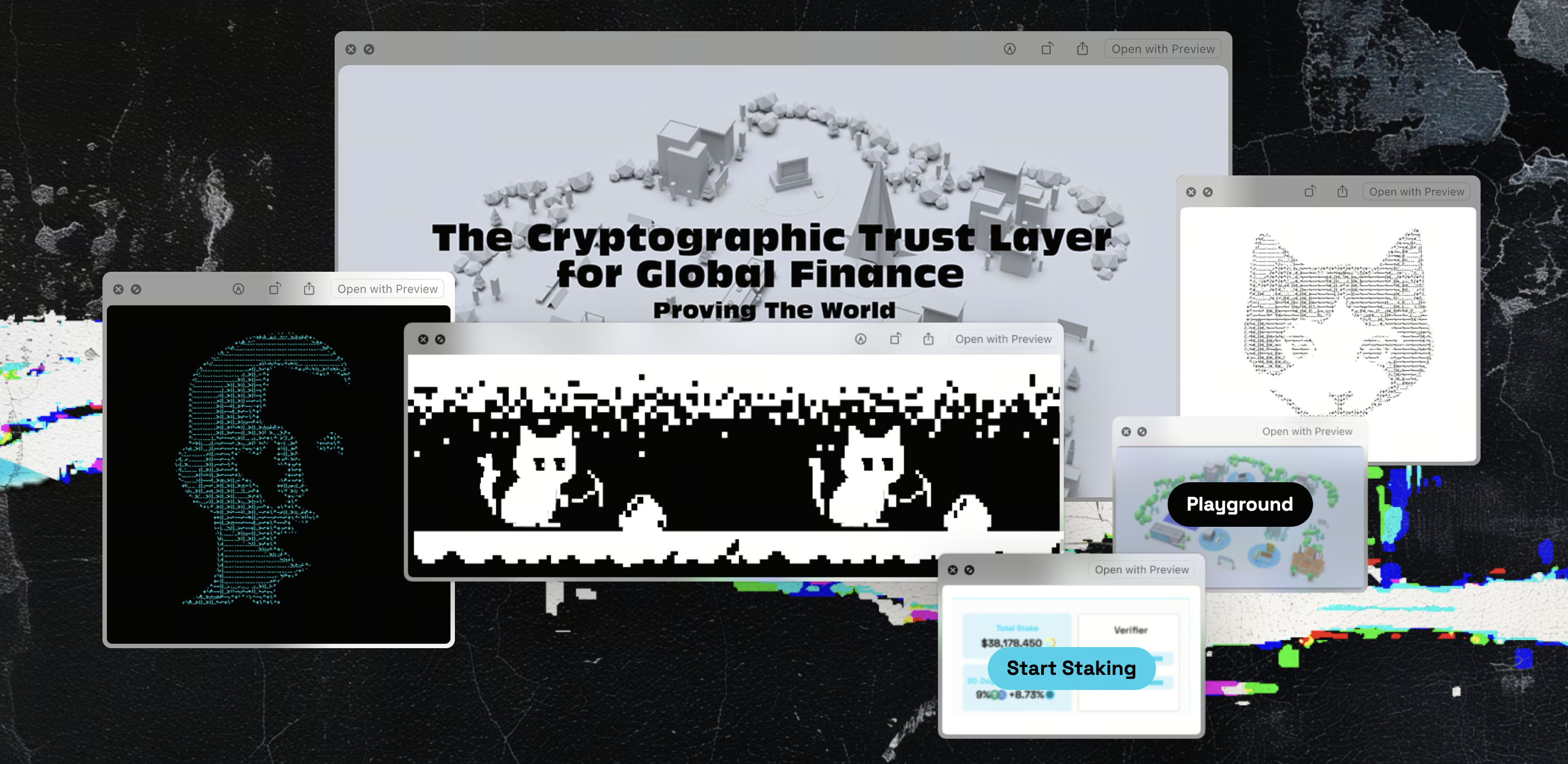
Source: zerobase.pro
What Is ZEROBASE
The core purpose of ZEROBASE is to build an infrastructure network that combines “data processing + computational execution.” Unlike a protocol focused only on data indexing or storage, it handles both data processing and computation verification.
This network can be understood as a “decentralized computing layer” built specifically to execute complex tasks and generate verifiable results. With this structure, developers can perform computation off chain while submitting the results on-chain in a verifiable form.
In this process, the “decentralized computing network” and “on-chain data infrastructure” together form its core capabilities, allowing it to support an integrated workflow from data queries to complex computation.
ZEROBASE’s Technical Architecture: Data Layer, Computing Layer, and Network Structure
ZEROBASE uses a multilayer architecture that separates different functions into independent modules to improve scalability and performance.
Overall, its architecture mainly consists of three layers:
-
Data layer: Responsible for data input, processing, and structuring
-
Computing layer: Executes tasks and generates zero knowledge proofs
-
Network layer: Coordinates nodes and task distribution
The network is coordinated through a HUB-Prover model:
-
HUB nodes are responsible for task scheduling and routing
-
Prover nodes are responsible for executing computation and generating proofs
In addition, TEE, or trusted execution environment, is used to protect the privacy of input data, so data is not exposed to node operators during processing.
This structure brings together “privacy + verifiability + high performance,” allowing the network to support large scale computing demand.
How ZEROBASE Works: Data Processing and Computation Flow
ZEROBASE operates as a standardized, task driven data processing and computation flow. At its core, it breaks complex computation into separate tasks and assigns them to a decentralized network for execution, while ensuring that the results remain verifiable.
First, users or applications submit data requests or computing tasks. These tasks may include on-chain data analysis, privacy computing, or complex logic processing. The tasks are then scheduled through the network’s coordination layer, such as HUB nodes, and distributed to suitable Prover nodes for execution. This reflects a typical “distributed computing flow,” allowing computing capacity to scale on demand.
During the execution stage, Prover nodes not only complete the task itself, but also generate the corresponding zero knowledge proof to prove the correctness of the computation result without exposing the original data. At the same time, data input is usually processed inside a trusted execution environment (TEE), further reducing the risk of data leakage.
Finally, the computation result and the corresponding proof are returned and can be verified on-chain. This closed loop of “computation + proof + verification” allows ZEROBASE to deliver efficient computation while also protecting privacy and preserving trust in the results.
Functions and Role of the ZBT Token: Incentives, Payments, and Network Security
ZBT is the core functional asset in the ZEROBASE network, and its role extends across three key areas: resource usage, incentive distribution, and security protection.
At the payment level, ZBT serves as the unit of account within the network and is used to pay for data processing and computation fees. When users submit tasks, they need to spend ZBT to access network resources, creating a market based relationship between supply and demand for computing power.
At the incentive level, nodes that participate in network operations, such as Prover nodes and coordination nodes, receive ZBT rewards for completing tasks. This mechanism ties rewards to actual computational contribution, encouraging nodes to continuously provide computing power and services. At the same time, introducing a staking mechanism, such as stablecoin staking, can help constrain node behavior and improve execution reliability.
At the security level, ZBT helps maintain stable network operation through incentive and penalty mechanisms. If a node behaves abnormally, for example by failing to complete a task or submitting an incorrect result, it may face reduced rewards or staking losses, creating an economic constraint. Overall, ZBT builds an economic system in which “usage, incentives, and constraints” are closely connected.
ZEROBASE Use Cases: From Data Services to AI and on-chain Analytics
ZEROBASE’s architecture allows it to cover a wide range of scenarios, from basic data services to advanced computing applications. It is especially suited to fields with strong requirements for privacy and verifiability.
At the foundational level, ZEROBASE can function as an on-chain data processing network, providing applications with data querying, processing, and structuring capabilities. These functions are similar to Web3 data infrastructure, but extend further into the computing layer, meaning the network can not only “read data,” but also “process data.”
In more complex use cases, its decentralized computing capabilities can support AI model related tasks, data analysis, and privacy computing. For example, when sensitive data needs to be analyzed without exposing the original information, zero knowledge proofs can verify the correctness of the computation result, enabling a form of data processing that is “verifiable but not visible.”
As a result, in financial analysis, on-chain behavior research, and compliance oriented data processing scenarios, ZEROBASE offers a path that balances efficiency, privacy, and trust.
How ZEROBASE Differs from Other Data Protocols: Comparison with The Graph, Filecoin, and Others
ZEROBASE differs clearly from other Web3 data protocols in its functional positioning.
For example, The Graph is mainly used for data indexing and queries, while Filecoin focuses on decentralized storage.
By comparison, ZEROBASE places greater emphasis on “computation + verification,” rather than data storage or indexing alone.
| Dimension | ZEROBASE | The Graph | Filecoin |
|---|---|---|---|
| Core function | Data processing + computation | Data indexing | Data storage |
| Supports computation | Yes | No | No |
| Privacy capabilities | ZK + TEE | None | Limited |
| Main use | Computation and verification | Data queries | Data storage |
As the comparison shows, ZEROBASE is positioned more as “decentralized computing infrastructure” than as a single purpose data protocol.
ZEROBASE’s Strengths, Limitations, and Common Misconceptions
ZEROBASE’s core strength lies in its ability to provide both “privacy protection” and “verifiable computation,” a combination that is relatively uncommon in traditional blockchain or data infrastructure. By combining zero knowledge proofs (ZK) with trusted execution environments (TEE), the system can prove the correctness of computation results without exposing the original data, making it suitable for scenarios with higher requirements for data privacy and compliance.
From a structural design perspective, its multilayer architecture, including the data layer, computing layer, and coordination layer, gives the network strong scalability and allows it to support complex computing tasks and diverse application scenarios. At the same time, the introduction of distributed computing and task scheduling mechanisms makes resource usage more flexible and can help improve overall computing efficiency.
However, this design also brings certain limitations. On one hand, zero knowledge proofs involve relatively high computational costs, which may affect performance in high frequency or large scale task scenarios. On the other hand, the multirole and multilayer structure increases system complexity, raising the barrier for both development and participation.
In addition, the system’s performance depends to some extent on node quality and network coordination. If task scheduling or node performance is unstable, overall efficiency may be affected. One common misconception is to view ZEROBASE as a “data storage network” or “data indexing protocol,” when its core value lies in computation and verification rather than simple data storage or query functions.
Summary
By combining zero knowledge proofs, decentralized computing, and on-chain verification mechanisms, ZEROBASE builds a new type of infrastructure for data processing and privacy computing. Its design is not focused on replacing traditional data services, but on creating a verifiable connection between trusted computation and privacy protection.
The core value of this system is “verifiable computation,” meaning computation results can be audited and trusted without exposing the underlying data. This expands the potential use of blockchain in data intensive and compliance focused scenarios.
Although challenges remain in performance costs, system complexity, and participation barriers, ZEROBASE provides a viable path for combining privacy computing with on-chain verification, offering a new design approach for the development of Web3 infrastructure.
FAQ
- Is ZEROBASE a data protocol or a computing network?
It is closer to a decentralized computing network, while also offering data processing capabilities.
- What is the role of the ZBT token?
It is used to pay computation fees, incentivize nodes, and maintain network operations.
- How is ZEROBASE different from The Graph?
The Graph mainly focuses on data indexing, while ZEROBASE provides computation and verification capabilities.
- How does ZEROBASE protect data privacy?
It uses zero knowledge proofs and trusted execution environments (TEE).
- Can it be used for AI computation?
Its architecture supports data processing and computing tasks, so it can be extended to AI scenarios.
Related Articles

The Future of Cross-Chain Bridges: Full-Chain Interoperability Becomes Inevitable, Liquidity Bridges Will Decline

Solana Need L2s And Appchains?

Sui: How are users leveraging its speed, security, & scalability?

Navigating the Zero Knowledge Landscape

What is Tronscan and How Can You Use it in 2025?


