The Law Already Inside Bitcoin
There is a standard story about Bitcoin and the law. It goes like this: Bitcoin was designed to work without governments. It replaces trust in institutions with trust in mathematics. It is permissionless — anyone can participate, no one can be excluded, and no central authority controls it. The system secures itself through the sheer cost of attacking it. Law is optional. Law is external. Law is what Bitcoin was built to avoid.
This story is wrong. Not completely wrong — there is a kernel of truth at the low end. But as a description of how Bitcoin actually works when real money is at stake, it is a fairy tale. And it is a fairy tale that has distorted how economists, regulators, and the crypto industry itself think about blockchain security.
The Economist’s Version
The most rigorous version of this story comes from economics, not from cypherpunk forums. The argument, stated cleanly, is this: in a permissionless system with no rule of law, the only thing preventing a double-spend attack is the cost of mustering enough computing power to outrun the honest chain. Security is a flow-cost problem. The network must spend enough, continuously, to make attacking it unprofitable. If the value of what you can steal exceeds the cost of the attack, the system is insecure.
This is a real result. It is mathematically correct within its stated assumptions. And it leads to a disturbing conclusion: securing high-value transactions on a proof-of-work blockchain requires enormous, ongoing resource expenditure proportional to the value at risk. If you want to settle a billion-dollar transaction, the network must be burning enough electricity and hardware to make a billion-dollar attack unprofitable. That is expensive. That looks wasteful. That looks like a fundamental economic limit.
But notice the load-bearing phrase: with no rule of law. The entire result depends on modelling the attacker as someone who operates in a legal vacuum — anonymous, untraceable, facing no consequences beyond the direct cost of the attack itself. That is not an incidental simplification. It is the central assumption. And it is factually wrong for every economically significant Bitcoin transaction that occurs in the real world.
Who Actually Mines Bitcoin
The story of anonymous miners hashing away in basements ended years ago. Bitcoin mining is an industrial activity. It is organised through mining pools — entities that coordinate block production, receive block rewards, and distribute payouts to contributing hash providers according to contractual rules.
As of March 2026, the five largest pools control over 70% of Bitcoin’s hashrate. The top two — Foundry USA and AntPool — together account for nearly half. These are not shadowy anonymous operations. Foundry USA is a subsidiary of Digital Currency Group. MARA Pool is operated by MARA Holdings, a NASDAQ-listed company that disclosed 400,000 mining rigs, 53 exahashes per second of computing power, and a Bitcoin treasury worth over four billion dollars in its most recent annual filing. These are companies with names, addresses, stock tickers, auditors, banking relationships, and legal counsel.
The coordination layer of Bitcoin mining — the set of entities that actually build blocks and distribute rewards — is concentrated in a small number of jurisdictions. U.S.-linked pools account for about 42% of hashrate. China-linked pools account for about 41%. Singapore, Japan, the Czech Republic, and Slovenia account for most of the rest. Less than 2% of hashrate comes from pools that cannot be publicly identified through coinbase tags, corporate filings, or disclosed operators.
This is not the picture of a system operating beyond the reach of law. It is the picture of an oligopolistic industry with a handful of identifiable actors operating in legally reachable jurisdictions. When economists model Bitcoin’s attacker as anonymous and legally untouchable, they are not describing this industry. They are describing a hypothetical that the industry left behind a decade ago.
What a Real Attack Looks Like
A double-spend attack on Bitcoin is not abstract. It works like this: an attacker sends Bitcoin to a counterparty — say, to an exchange in return for dollars — and simultaneously begins secretly mining an alternative version of the blockchain that does not include that transaction. If the attacker’s secret chain grows longer than the public chain, it replaces it, and the original payment disappears. The attacker keeps both the dollars and the Bitcoin.
For this to work at any meaningful scale, the attacker needs to control a majority of mining power for a sustained period. In today’s network, that means controlling more than 400 exahashes per second. No individual can do this. The only plausible route to a majority attack runs through the pool layer — either a single large pool deviating from honest mining, or a coordinated group of pools colluding.
Now ask: what happens to that pool after the attack?
The attacker — a named, publicly listed company or a well-known pool brand — has just defrauded a specific counterparty. The double-spend victim knows they were cheated. The blockchain record shows which pool built the attacking chain (coinbase tags make this visible). The exchange that was defrauded has legal counsel, insurance, and regulatory relationships. The pool depends on those same exchanges to convert mining revenue into fiat currency.
The attacker is not anonymous. The victim is not helpless. And the system that connects them is not lawless.
The Enforcer Participation Constraint
Here is where the standard economic story gets something half right. For trivial transactions — a five-dollar coffee, a twenty-dollar online purchase — nobody is going to sue. The cost of legal action exceeds the loss. A lawyer costs more than the coffee. In that range, law really is irrelevant, and protocol-level security is all that matters. The pure economic model applies.
But legal irrelevance does not scale with transaction value. It scales against it. A five-million-dollar double spend against an identified pool operator with seized assets and exchange-held balances is a different matter entirely. That is wire fraud. That is computer fraud. That is the kind of case prosecutors take, insurance companies pursue, and exchanges cooperate on.
The real question is not whether law exists that covers double spending — it does. The question is whether anyone will bother to invoke it. For small amounts, no. For large amounts, yes. There is a threshold — call it the enforcer participation constraint — below which the cost of legal action exceeds the expected recovery, and above which it becomes worthwhile.
Recent enforcement actions in the crypto sector provide a rough sense of where that threshold sits. Binance paid $4.3 billion to settle charges with the DOJ, FinCEN, and OFAC. FTX and Alameda reached a $12.7 billion settlement with the CFTC. BitMEX settled for $100 million. These were for compliance failures, not double-spend attacks. A deliberate double spend — an act of outright fraud against specific victims — would attract criminal charges carrying imprisonment and asset forfeiture on top of civil liability.
The implication is straightforward. For small transactions, the no-law model is correct. For large transactions, it is not. And the boundary between them is not at the billion-dollar level. It is somewhere in the low single-digit millions, depending on the jurisdiction, the institutional capacity of the victim, and the identifiability of the attacker. For pool-mediated attacks, identifiability is close to 100%.
Why Pooled Attacks Fall Apart
Even before law enters, a pooled attack has a structural fragility that the standard model ignores: the pool depends on other people’s machines.
A mining pool operator coordinates block production, but much of the actual computing power comes from outside contributors — firms and individuals who point their hardware at the pool in exchange for a share of rewards. These contributors can leave at any time. They are in the pool for the money. If the pool’s payouts deteriorate, they switch to a competitor.
A hidden double-spend attack degrades payout quality. The pool is diverting hash from honest mining to a secret chain that, if it fails, earns nothing. Contributors see lower payouts, higher variance, more stale shares. They do not need to know an attack is underway. They just see that the pool is performing worse than alternatives. They leave.
Once the attack is detected or suspected, a second exit channel opens. Contributors who stay risk being associated with fraud. Their hardware may be tainted. Their exchange accounts may be scrutinised. Their contracts with hosting providers may be at risk. For a firm operating hundreds of millions of dollars in specialised mining hardware, the rational response to a pool being publicly linked to an attack is to leave immediately and distance yourself from the operation.
And there is a further point often missed: if the attack fails — if the honest chain remains longer — the attacker loses everything it spent building the secret chain. The honest miners do not need to do anything special. They just keep mining. The Nakamoto protocol’s longest-chain rule does the rest. Honest hash that exceeds attacker hash means the attacker’s chain is orphaned. The protocol itself is the exclusion mechanism. Honest miners are not forming a coalition or mounting a defence. They are doing what they always do. The attacker is the one who must do something extraordinary — and sustain it — while its own coalition bleeds members.
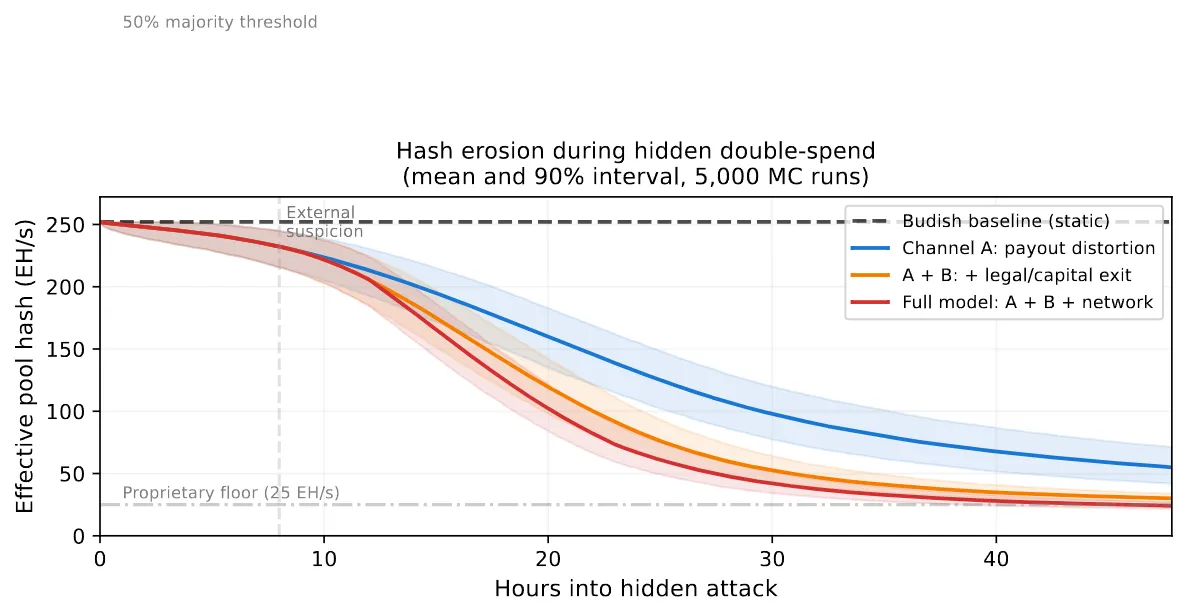
The result is that the attacking pool’s capacity is not fixed. It erodes during the attack. Simple simulations of this dynamic show that a pool starting with 31% of network hashrate can lose the majority of its contributed hash within hours once payout distortion becomes observable. The pool converges toward its proprietary hash — the machines it actually owns — which for most pools is a small fraction of total capacity. An attack that looked feasible at the nominal level becomes infeasible as contributors flee.
The Capital Problem
There is a deeper issue that the standard model misses entirely: capital specificity.
Bitcoin mining hardware — ASICs — is not general-purpose equipment. A Bitcoin ASIC does one thing: compute SHA-256 hashes. It cannot mine Ethereum. It cannot be repurposed as a web server. It cannot run machine learning workloads. If you are excluded from profitable Bitcoin mining, your hardware is worthless. It is scrap metal with a power connector.
A major pool operator has billions of dollars in ASIC hardware, hosting contracts, power agreements, and a Bitcoin treasury. MARA Holdings alone disclosed over five billion dollars in combined ASIC fleet and Bitcoin holdings. Foundry USA aggregates contributed hash from dozens of firms, each with its own capital exposure. A successful double spend might net the attacker tens of millions of dollars. But the capital at risk from being identified, sanctioned, and excluded is measured in billions.
This is not a flow-cost problem. It is a stock-cost problem. The attacker is not risking a few days of forgone mining revenue. It is risking the productive value of a capital base that has no alternative use. That changes the economics fundamentally. In the standard model, security requires continuous expenditure proportional to the value at risk. In the world of identifiable, capital-intensive pool operators, security is backstopped by the threat of permanent capital destruction.
The irony is that the original economic critique recognises how powerful stock-cost deterrence would be — if only it existed. The argument is that proof-of-work lacks it, because attacking hash can be rented, deployed, and discarded. That was approximately true in 2012. It is not true in 2026. Mining is now a capital-intensive industry with fixed infrastructure, long-dated power contracts, and hardware that cannot be repurposed. The stock cost exists. The economic model just has not caught up.
Two Regimes, One System
What emerges is not a rejection of the economist’s model but a localisation of it. Bitcoin does not have a single security regime. It has two, operating simultaneously.
For small transactions — the vast majority by count — protocol-only security applies. Each transaction is too small to justify legal process, and the system relies on the cost of assembling attacking hash. This regime works. It is what the standard model describes. And it is compatible with high aggregate throughput: a system processing millions of small payments can operate entirely within the protocol-only regime, with low per-transaction security costs.
For large transactions — individually valuable enough to make legal enforcement economic — a second regime takes over. The attacker’s payoff is no longer determined by protocol costs alone. It is reduced by expected legal sanctions, exchange freezes, monetisation frictions, reputational destruction, capital impairment, and the endogenous erosion of the attacking coalition as contributors exit. In this regime, the pure flow-cost model overstates attack profitability because it ignores everything that happens to an identified attacker after the blockchain mechanics play out.
The two regimes are not in tension. They are complementary. The protocol-only regime handles the volume. The law-and-organisation regime handles the value. Together, they produce a security environment that is substantially more robust than either one alone.
The Real Lesson
The deeper point is not about Bitcoin specifically. It is about how we think about technology and institutions.
The cypherpunk narrative frames law and protocol as substitutes — you can have one or the other, and the whole point of Bitcoin is to choose protocol. The economic critique accepts that framing and asks whether the protocol can do the job alone. Both sides are arguing within the same false dichotomy.
In practice, protocol and law are complements. The protocol provides the base layer: transaction ordering, immutability, censorship resistance, and a cost structure that deters casual attacks. Law provides the upper layer: identity, accountability, sanctions, recovery, and a cost structure that deters serious attacks by serious actors. Neither layer is sufficient alone. Together, they cover the range.
This should not be surprising. No valuable economic system in history has operated entirely outside the reach of legal institutions. Not banking. Not securities markets. Not insurance. Not telecommunications. Not the internet itself, which was also once hailed as a space beyond government. The question was never whether law would reach Bitcoin. The question was when, and through which channels. The answer is: it already has, through the industrial structure of mining itself.
The miners did not need to be regulated into compliance. They regulated themselves into visibility by the simple economic logic of pooling, specialisation, and scale. The same forces that made mining efficient — risk-sharing through pools, capital investment in ASICs, exchange relationships for monetisation — are the forces that made mining legible. And legibility is all that law requires.
Bitcoin’s security does not depend on being beyond the law. It depends on being embedded in it. The protocol handles the small stuff. The law handles the big stuff. And the industrial structure of mining — pools, ASICs, exchanges, listed companies, jurisdictional concentration — is what connects them. That structure was not imposed by regulators. It emerged from the economics of mining itself. And it is the single most important fact about Bitcoin security that the standard economic critique gets wrong.
Disclaimer:
-
This article is reprinted from [Craig’s Substack]. All copyrights belong to the original author [Craig Wright]. If there are objections to this reprint, please contact the Gate Learn team, and they will handle it promptly.
-
Liability Disclaimer: The views and opinions expressed in this article are solely those of the author and do not constitute any investment advice.
-
Translations of the article into other languages are done by the Gate Learn team. Unless mentioned, copying, distributing, or plagiarizing the translated articles is prohibited.
Related Articles

In-depth Explanation of Yala: Building a Modular DeFi Yield Aggregator with $YU Stablecoin as a Medium

BTC and Projects in The BRC-20 Ecosystem

What Is a Cold Wallet?

Blockchain Profitability & Issuance - Does It Matter?
What is the Altcoin Season Index?


