Blast to Layer 2 multi-signature backdoor: which is more important, technology or social consensus
Author: Faust, geek web3
Introduction: Blast’s subtext in the face of orthodox Layer2 such as Polygon zkEVM may be "Princely generals, would you rather have a kind of?"Since everyone is not trusting enough, the essence of **** is to rely on social consensus to ensure safety, so why bother criticizing Blast’s Layer2 concentration is not high enough, “why is it too anxious”?
Admittedly, Blast’s reliance on 3/5 multisig to control deposit addresses has been widely criticized, but most Layer 2s also rely on multisig to manage contracts, and Optimism has even used only one EOA address to control contract escalation privileges. At a time when mainstream Layer 2 almost all have security risks such as multi-signature, slamming Blast for not being safe enough is more like the technical elite’s “disdain” for a gold-mining project.
But putting aside the above two merits, the significance of the existence of blockchain is more to solve the problem of information opacity in social consensus/democratic governance, and when advocating the supremacy of technology, we must admit that social consensus itself is more important than technology, because it is the foundation that guarantees the effective operation of all Web3 projects. In the final analysis, technology is in the service of social consensus, and projects that cannot be recognized by most people, no matter how superior the technology is, are essentially just a gorgeous appendix.
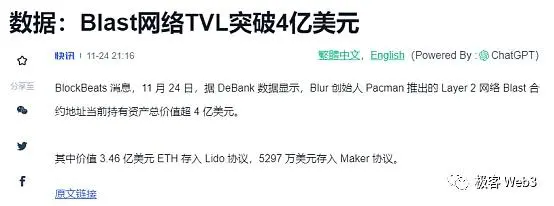
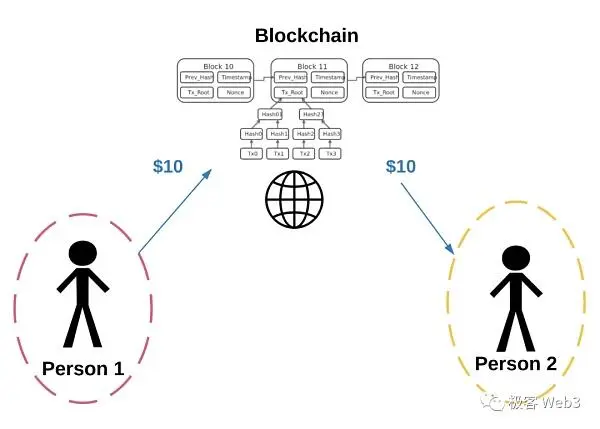
Text: Recently, the new project Blast launched by the founder of Blur has become popular all over the network, this “asset interest” protocol under the banner of Layer 2 has set up a deposit address on the ETH chain, and after users deposit funds into the Blast address, these funds will be used for native staking of the ETH network, placing them in MakerDAO to earn interest, etc., and the profits will be returned to users.
Relying on the aura of the founder itself and the attractive gameplay, Blast received $20 million in financing from investors led by Paradigm, and also attracted the participation of countless retail investors. **Less than 5 days after its launch, Blast top-up addresses attracted more than $400 million in TVL. It is no exaggeration to say that BLast is like a strong medicine in a long bear market, which instantly aroused people’s frenzy.
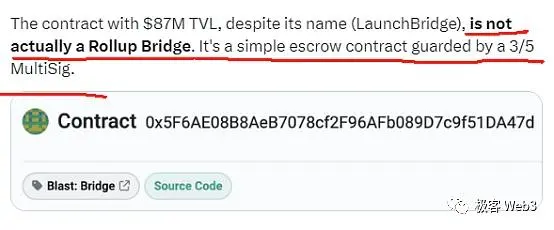
However, while Blast has achieved phased success, it has also attracted many experts’ doubts. For example, L2BEAT and Polygon engineers have all said that the current Blast is just a deposit contract deployed on Ethereum, and this contract can be upgraded under the control of 3/5 multisig, in other words, the code logic of the contract may be rewritten, and Rug can still be Rug. At the same time, Blast only claims to implement a rollup structure, but now it is just an empty shell, and even the withdrawal function will not be launched until February next year.
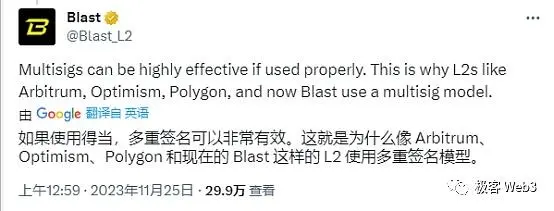
And Blast is also unbearable to show weakness, **The vast majority of Rollups rely on a set of multi-signature management contracts behind them to upgrade their permissions, and other Layer2 accuses “Blast with multi-signature” is just 50 steps and 100 steps. **
Layer2 multisig is a long-standing problem
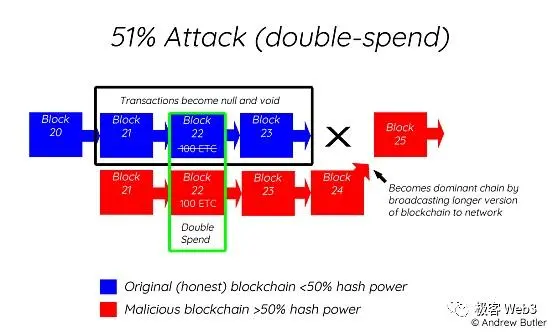
In fact, multi-signature of Layer 2 contracts has been a long-standing problem. As early as July this year, L2BEAT conducted a special investigation on the upgradeability of the Rollup contract, and the so-called “upgradeable” is to change the logical contract address pointed to by the proxy contract to achieve the effect of changing the contract logic. **If the new contract contains malicious logic, Layer 2 can steal the user’s assets.

(图源:wtf academy)
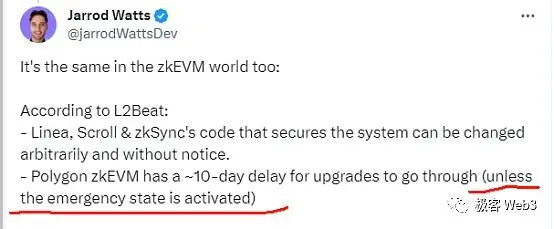
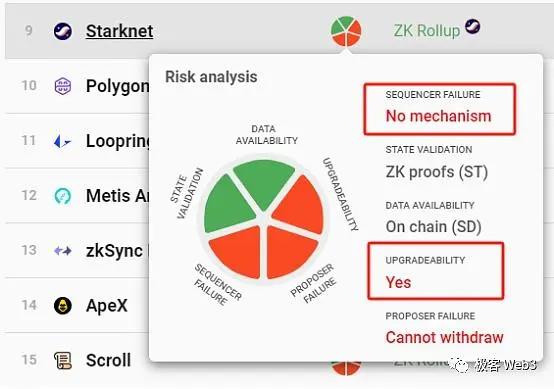
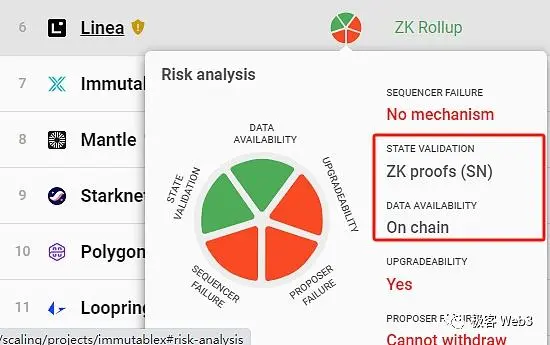
According to L2BEAT’s data, at present, mainstream rollups such as Arbitrum, Optimism, Loopring, ZKSync Lite, ZkSync Era, Starknet, and Polygon ZKEVM have adopted multi-signature authorized upgradeable contracts, which can be upgraded immediately by bypassing the timelock limit. **

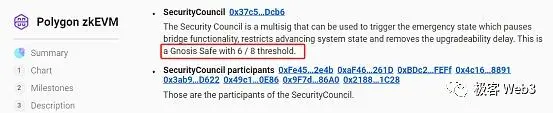
Surprisingly, Optimism used to only use an EOA address to manage the contract upgrade, and even the multisig was only added in October this year. As for the **Polygon zkEVM, which has attacked Blast, it can also carry out an “emergency takeover” of the Rollup contract under the authorization of 6/8 multi-signature, and change Layer 2 from contract governance to “naked human governance”. Interestingly, this was also mentioned by the Polygon engineer who criticized Blast above, but in a vague manner.
So what is the significance of the existence of this “emergency mode”?**Why do most rollups have to leave themselves a panic button or backdoor?**According to Vitalik’s previous statement, Rollups need to frequently update the contracts deployed on ETH during the iteration process, and it is difficult to iterate efficiently without introducing upgradeable means such as proxy contracts.
In addition, smart contracts that host a large number of assets may have bugs that are not easily detected, and it is inevitable that the Layer 2 development team will be negligent and if some vulnerabilities are exploited by hackers, it could lead to the theft of large amounts of assets. Therefore, whether it is a Layer 2 or a DeFi protocol, a panic button is often set up, and “committee members” intervene when necessary to prevent some vicious events from happening. **
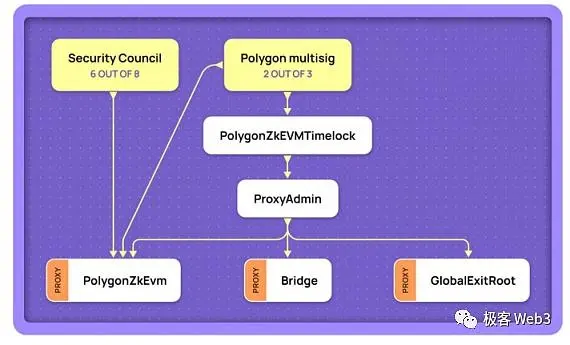
Of course, Layer 2 committees can often bypass timelock restrictions and immediately upgrade contract code, but from a certain point of view, they seem to be more taboo than hackers and other external factors. In other words, in any case, it is difficult for a smart contract that hosts a huge amount of assets to be exempt from a certain degree of “trust assumption”, that is, the assumption that the multisig controller behind the contract does not do evil. Unless the contract is designed to be non-upgradeable and there are no bugs that could threaten the security of the user’s assets.
The reality is that mainstream Layer 2s either allow their own committees to update contracts immediately, or introduce shorter timelock restrictions (e.g. anyone who wants to upgrade the dYdX contract has a delay of at least 48 hours). If it is discovered that the committee intends to add malicious logic of stealing assets to the new version of the contract code, the user will theoretically have enough time to react and urgently withdraw the assets from Layer 1. **
(A timelock is a delay that allows you to perform certain operations)
But the crux of the problem is that many Layer 2s don’t even have a forced withdrawal function that can bypass the Sequencer sequencer, so the Layer 2 official can do evil by letting the sequencer reject everyone’s withdrawal request first, and then transfer the user’s assets to the L2 account controlled by the Layer 2 official. After that, the official will update the Rollup contract according to its own needs, and when the timelock delay is over, all user assets can be transferred to the ETH chain.
Of course, the actual situation may be worse than I said, because most rollups can upgrade contracts without timelocks, which means that they can complete hundreds of millions of dollars of rugs almost instantly.
A truly trustless Layer 2 should make the contract upgrade delay greater than the forced withdrawal delay
In fact, in order to solve the trustless/security problem of Layer 2, the following things need to be done:
By setting up a censorship-resistant withdrawal outlet on Layer 1, users can directly transfer assets from Layer 2 to the ETH chain without the permission of the sequencer. The delay of forced withdrawal should not be too long, so as to ensure that the user’s assets can be quickly withdrawn from L2;
Anyone who wants to upgrade a Layer 2 contract must be subject to a timelock delay limit, **contract upgrade should take effect later than the mandatory withdrawal. **For example, if there is a delay of at least 48 hours for the contract upgrade of dYdX, then the delay for the mandatory withdrawal/escape pod mode should be reduced to 48 hours. In this way, after the user finds that the dYdX project party wants to dope the new version of the contract with malicious code, he can withdraw the assets from Layer 2 to Layer 1 before the contract is updated. **
At present, the vast majority of rollups that have launched the forced withdrawal/escape pod mechanism do not meet the above conditions. For example, dYdX’s forced withdrawal/escape pod has a maximum delay of 7 days, but the contract upgrade delay of the dYdX committee is only 48 hours, which means that the ** committee can complete the deployment of new contracts before the user’s forced withdrawal takes effect, and steal the assets before the user escapes. **

From this point of view, except for Fuel, ZKSpace, and Degate, other rollups cannot guarantee that the user’s forced withdrawal will be processed before the contract is upgraded, and there is a high degree of trust assumption.
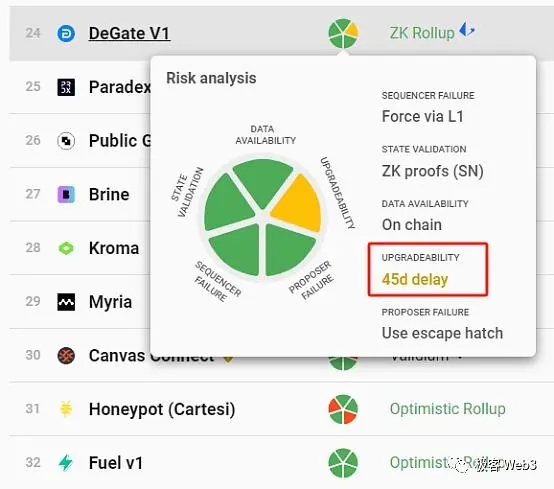
Many projects that adopt the Validation scheme (DA is implemented off-chain on Ethereum) have a long contract upgrade delay (e.g., 8 days or more),** but Validium often relies on off-chain DAC nodes to publish the latest data, and DACs may launch data withholding attacks that invalidate forced withdrawals, so they do not meet the security model discussed above. **
At this point, it seems clear and concise to conclude that none of the Layer 2 solutions, with the exception of Fuel, ZKSpace, and DeGate, are trustless. Users either trust the Layer 2 project or the security committee set up by it not to do evil, or trust the DAC nodes off the chain not to collude, or trust the sequencer not to review your transaction (reject your request). There are only 3 Layers 2 that truly meet the requirements of security, censorship-resistant, and trustlessness.
Security is not only achieved by technology, but must introduce social consensus
In fact, the topic we are talking about today is not new, and the essence of Layer 2 pointed out in this article depends on the credibility of the project party has been pointed out by countless people for a long time. For example, Avalanche and the Solana founders have lashed out at this, but the problem is that these trust assumptions that exist in Layer 2 also exist in Layer 1 and even in all blockchain projects. **
For example, we need to assume that the validator nodes that account for 2/3 of the stake weight in the Solana network do not collude, and we need to assume that the top two mining pools, which account for the majority of Bitcoin’s hash power, do not join forces to launch a 51% attack to roll back the longest chain. While these assumptions are hard to break, “hard” doesn’t mean “no.”
Once the traditional Layer1 public chain has an evil behavior that causes damage to a large number of user assets, it will often abandon the problematic chain and fork a new chain through social consensus (refer to the 2016 The DAO incident that led to the fork of Ethereum into ETH and ETC). If someone tries to make a malicious fork, everyone should also choose which “more reliable” fork to follow through social consensus. (For example, most people do not follow the ETHW project)
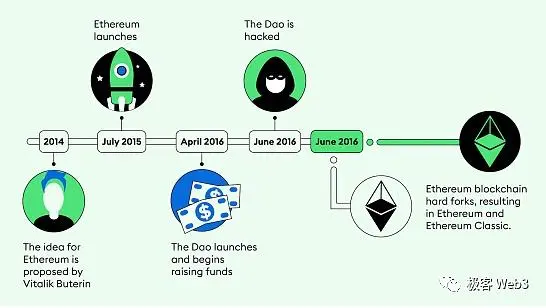
Social consensus is the root cause of ensuring the orderly operation of blockchain projects and even the DeFi protocols they carry, and even error correction mechanisms such as contract code audits and community members disclosing problems in a project are also part of social consensus. However, decentralization, which is achieved solely by technology, often does not play the greatest role, and many times stays at the theoretical level.
What really plays a role at a critical moment is often a social consensus that has nothing to do with technology, a public opinion supervision that has nothing to do with academic papers, and a mass recognition that has nothing to do with the technical narrative. **
We can imagine the following scenario: a POW public chain that only a few hundred people have heard of is temporarily in a highly decentralized state, because there is no dominance of one company. However, if a mining machine company suddenly invests all its computing power into the POW chain, the computing power of itself is many times higher than that of all other miners, and at this time, the decentralization of the POW chain will be disintegrated instantly. If the mining machine company intends to do evil, people can only correct the mistake through social consensus. **
On the other hand, the so-called Layer 2, no matter how elaborate its mechanism design, cannot avoid the link of social consensus, even L2 such as Fuel, DeGate, and ZKSpace, which are almost impossible for officials to do evil, ** the Layer1-Ethereum on which they rely is highly dependent on social consensus/community-public opinion supervision. **
MOREOVER, WE BELIEVE THAT THE CONTRACT IS NOT UPGRADEABLE, BECAUSE WE HAVE LISTENED TO THE STATEMENTS OF THE CONTRACT AUDITORS AND L2BEAT, BUT THESE INSTITUTIONS MAY BE NEGLIGENT OR LIE. Although this probability is extremely low, we have to admit that ** still introduces a small trust assumption to it. **
However, the open-source nature of the blockchain itself allows anyone, including hackers, to check whether the contract contains malicious logic, which actually minimizes the trust assumption, which greatly reduces the cost of social consensus. If this cost is reduced low enough, we can assume that this is “trustless”.
Of course, in addition to the three mentioned above, the other Layer2 does not have the so-called trust at all, and what really guarantees security at critical moments is still social consensus, and the technical component is often just convenient for people to carry out social consensus supervision. If a project is technically superior, but not widely recognized and unable to attract a large community, then its decentralized governance and social consensus itself will not be effective in carrying out effectively.
Technology is important, but more often than not, the ability to be widely recognized and the ability to develop a strong community culture is a more important, more valuable, and more conducive factor to the development of the project than technology. **
We might as well take zkRollup as an example, at present, many zkRollups only implement the validity proof system and DA data on the chain, which can prove that all the user transactions and transfers they process are valid, not forged by the sequencer, and there is no evil in the matter of “state transition”, but there is not only one scenario in which the Layer2 official or sequencer is evil.
We can approximate that the ZK proof system essentially only greatly reduces the cost of people’s supervision of Layer 2, but there are many things that cannot be solved by technology itself, and must rely on the intervention of human governance or social consensus.
If the L2 official does not set up censorship-resistant exits such as forced withdrawals, or if the official tries to upgrade the contract and mix it with the logic that user assets can be stolen, community members will have to rely on social consensus and public opinion fermentation to correct their mistakes. At this moment, it seems that the superiority of technology is no longer the most important, not so much whether technology is important for security, but rather that the mechanism design itself that is convenient for people to carry out social consensus is more important, which is actually the true meaning of Layer2 and even blockchain. **
From Blast, which is supervised solely by social consensus, we should look more directly at the relationship between social consensus and technical implementation, rather than judging the merits of a project based on “which L2 is closer to Layer 2 in vitalik’s mouth than the other”. When a project has gained the approval and attention of millions of people, a social consensus has been formed, and it doesn’t matter whether it’s a marketing or a technical narrative, because the outcome itself is more important than the process.
It is true that social consensus itself is an extension of democratic politics, and the real world has confirmed the defects of democratic governance, but the open source and data transparency that comes with the blockchain itself greatly reduces the cost of social consensus, so the “rule of man” of Web3 is essentially different from the “rule of man” of real sovereign countries. **
** If we look at blockchain itself as a technical means to improve the issue of information transparency in democratic governance, rather than simply pursuing the never-ending “trustless implementation of code”, everything seems to be much more optimistic and clear. Only by getting rid of the arrogance and prejudice fixed by the technical elite and embracing a wider audience can the Ethereum Layer2 system truly become a world-class financial infrastructure for mass adoption.